Dark Web: Accessing the hidden content Part- 2
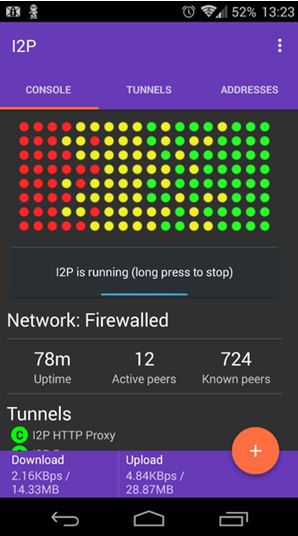
I2P Intro: According to Wikipedia, The Invisible Internet Project (I2P) is an anonymous network layer that allows for peer to peer communication via encrypting the user’s traffic and sending it through a volunteer-run network of roughly 55,000 computers distributed around the world. The software that implements this layer is called an “I2P router” and a computer running I2P is called an “I2P node“. I2P is free and open source. I2P can be run both on Pc as well as android, here is a screeshot of I2P running on android device. Image source: https://en.wikipedia.org/wiki/File:I2PAndroid-console-0.9.20.png While tor lets you being anonymous and open sites hosted either publicly or dark sites ( with .onion) I2P’s focus on the other hand is creating its own internal internet is that the network isn’t accessible from a regular computer. By installing the requisite I2P software, your computer can join I2P and begin routing traffic, just like a Tor middle relay as it creat...
